- Home
- /
- Clients
- /
- Case Studies
- /
- UPS Case Study
Next steps:
Events:
Conference 2014
The Connected Enterprise – Cloud, Mobile, and the Internet of Things
Rome, Italy, December 2-3, 2014
Scheduled seminars
The New Integration Manifesto: Applications, Data, Cloud, Mobile, and the Internet of Things
October 27-28, 2014
Application Development in the Age of Cloud and Mobile
December 11-12, 2014
Case Study: Application & System Monitoring and Management Strategy

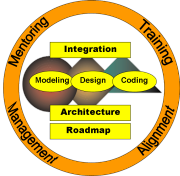
UPS is one of the largest logistics companies. The Service Oriented Architecture of the company has to support a multitude of external customers (B2B). The B2B transactions had to be integrated with back-end applications, which were made accessible to external clients trough wrappers. The same back-end applications were also accessed by internal users, resulting in a complex IT environment that was regulated by a number of Service Level Agreements (SLAs) mandated by the different user constituencies.
It became crucial to develop a monitoring and management strategy that would span all levels – from Application and Infrastructure Management (AIM), over Business Service Management (BSM), to Business Activity Monitoring (BAM). ISG developed a 4-phase strategy that guided the company though a controlled evolution of its monitoring and management capabilities.
Phase 1 consisted of ad-hoc monitoring of applications, integration points, and data. Disparate tools were used to monitor the IT infrastructure (i.e. system software, hardware, network). In the second phase, EAI tools were employed to consolidate monitoring & management functions on the application and business process side, and ESM tools consolidated the IT infrastructure management. In phase 3, a Business Process Management (BPM) tool was designed to allow monitoring and managing a business process as it unfolds step by step. At the same time, a BSM tool provided a new perspective on the performance of the IT environment from a business point of view. Finally, in the last phase of the program, it was envisioned that a BAM tool would help to exploit information gleaned from the IT environment in order to monitor the performance of the business itself.